Safety Through Standards
- Published: May 02, 2007, By By Joseph Pearson, Texas Instruments
May Web Exclusive
A growing number of counterfeit, gray market, and diverted products are entering the pharmaceutical supply chain, compromising consumer confidence in the authenticity of their prescription drugs. Radio Frequency Identification (RFID) technology is poised to help secure the supply chain, but to do so, the industry needs Item-Level Tagging standards, regulatory guidance from the federal government, and alignment on a Tag Data Security Infrastructure (TDSI).
The TDSI is a set of rules, specifications and common protocols that enable item-level tags and readers to work within and across the industry’s information technology ecosystem. RFID technology, when combined with a secure tag and data infrastructure, can assure both package authenticity and pedigree while creating new revenue opportunities. But while manufacturers, distributors, and retailers are collaborating on RFID pilot programs, they’re not yet in agreement on how to deploy this technology.
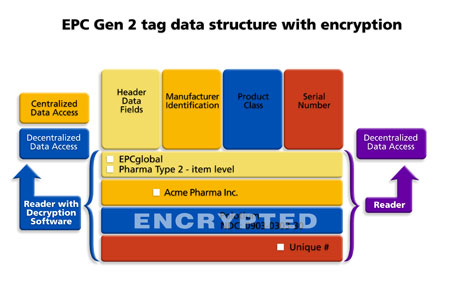
One central issue is whether RFID data should be centralized, decentralized, or some combination of the two. Should product information be associated with the tag on-network or off-network? If product information is on the tag, how can we protect a consumer’s privacy? The ultimate success of either or both of these deployment options, I believe, is likely to depend on a Tag Data Security Infrastructure.
The industry currently is working on developing a new Item-Level Tagging standard. This article proposes requirements for Item-Level Tagging deployment and lays the foundation for a TDSI for these initiatives. It defines the key deliverables and outlines the requirements of this common-ground approach. The TDSI is designed to expand and unify the industry’s information technology ecosystem by incorporating both centralized and decentralized deployment options.
Infrastructure Offers Choice & Flexibility
A TDSI will provide the broadest and most flexible approach for a secure supply chain, encompassing all of the stakeholder requirements, while providing an array of options for implementation. Having a choice of deployment methods within a so-called “standard” item-level tagging infrastructure is not a contradiction. The TDSI supports all network-based applications. It also bridges the centralized/decentralized infrastructure divide that exists among pharmaceutical sectors by augmenting network-based applications with the capability of anytime, anywhere authentication and product information.
The TDSI also addresses the contentious points of whether or not to put product data, such as the National Drug Code, on the tag, how to authenticate products, ways of ensuring consumer privacy, and how to secure tagged products at the item, pallet, and case level.
At this point, there is no common item-level tagging standard. As such, it’s an auspicious time for RFID tag, reader, and security technology providers to propose a solution as the industry considers the issues of specifications, rules, and methods of supply chain collaboration in the EPCglobal Inc. (epcglobalinc.org) standards development process.
How the TDSI Works
The cornerstone for pharmaceutical product identification is an Electronic Product Code (EPC) number programmed on the tag. The TDSI is able to accommodate network and off-network capabilities in order to support the pharmaceutical supply chain infrastructure. For example, to answer the question of whether product data should reside on the tag or off the tag, the TDSI is versatile enough to accommodate both situations. It provides options as to how the EPC number contains product data. It can be either encrypted on the tag or accessed through a network link.
For an EPC numbering scheme using an encrypted Serialized Global Trade Identification Number, the product data portion of the tag’s EPC number is digitally scrambled and can only be decrypted by a reader with the appropriate corresponding cryptographic software. The product information then is available for local applications, such as smart shelves. The EPC number still can be used as a unique pointer for network applications, like item-level ePedigree, because it retains its uniqueness. Any standard reader can read the 96-bit EPC number from an encrypted tag and forward it to the EPCglobal Network as a “pointer.” In addition, readers equipped with the verification key can both authenticate the tag and decrypt the product class portion of the EPC number off-network.
Elliptic Curve Cryptography
A standardized cryptography method is a central component of the TDSI, for both tag data encryption/decryption and authentication. The Inst. of Electrical and Electronic Engineers (IEEE) has developed the IEEE Standard 1363a Elliptic Curve Cryptographic (ECC) algorithm as a new standard for public-key cryptography. The National Security Agency has selected ECC as key technology for protecting mission-critical national security information. For RFID applications, ECC allows very rapid signature creation, ensuring no incremental delays in production line operation. This algorithm provides a level of security equivalent to 1,024-bit RSA encryption, but uses three-quarters less tag memory for a digital signature. In addition, ECC’s efficiency provides a high level of security to supply chain RFID tags but does not increase complexity, cost, or computing power.
Industry Alignment on a TDSI
The TDSI is designed for flexible and secure item-level tagging deployment throughout the supply chain. But for it to become reality, all key parties—pharmaceutical manufacturers, distributors, and retailers—must come to agreement on the rules, methods of deployment, and specifications.
From a technical point of view, the groups working on defining the EPC Item-Level Tagging specification for High Frequency and Ultra-High Frequency could consider adopting the IEEE Standard 1363a ECC algorithm. To make the hardware infrastructure available to the industry, RFID solution providers such as reader manufacturers would have to incorporate this standard into their devices as part of their product offerings.
In parallel with the introduction of the Gen 2 specification, EPCglobal established a certification procedure to address both compliance and interoperability. EPCglobal’s role in establishing an item-level specification should extend to the selection of a certifying authority for the public-key cryptographic infrastructure. The role of this group would be to issue certificates to authorized supply chain participants and manage the allocation of private and public keys.
Although outside the scope of the TDSI, additional security measures could be considered in the Item-Level Tagging standard. Examples include password read/write and/or a kill command, which would completely deactivate a tag.
This approach to Item-Level Tagging in an open yet secure supply chain is relevant not only to the pharmaceutical industry but also to everything from antiques and art to cosmetics, branded apparel, and even sports collectibles. The cornerstone of the TDSI system in the pharmaceutical market is that consumers can be better assured that they are getting safe and authentic products. In all these applications, consumer benefits from a secure RFID come in the form of raising the level of confidence that they are getting the genuine goods.
Joseph Pearson is a business development manager for the RFID Systems group at Texas Instruments Inc., Dallas, TX. He can be reached at j-pearson2@ti.com; 800/962-7343; ti.com.